Generate An Ssh Key Github
SSH keys come in pairs, a public key that gets shared with services like GitHub, and a private key that is stored only on your computer. If the keys match, you're granted access. The cryptography behind SSH keys ensures that no one can reverse engineer your private key from the public one. Generating an SSH key.
Log into your Github's account. In the top right corner of any page, click your profile photo, then click Settings. In the user settings sidebar, go to SSH and GPG keys. Click New SSH key. I need to do the SSH key audit for GitHub, but I am not sure how do find my RSA key fingerprint. I originally followed a guide to generate an SSH key on Linux. What is the command I need to enter to. Open your security settings by browsing to the web portal and selecting your avatar in the upper right of the user interface. Select Security in the menu that appears. Select SSH public keys, and then select + New Key. Copy the contents of the public key (for example, idrsa.pub) that.
There are four ways to manage SSH keys on your servers when automating deployment scripts:
- SSH agent forwarding
- HTTPS with OAuth tokens
- Deploy keys
- Machine users
This guide will help you decide what strategy is best for you.
SSH agent forwarding
In many cases, especially in the beginning of a project, SSH agent forwarding is the quickest and simplest method to use. Agent forwarding uses the same SSH keys that your local development computer uses.
Pros
- You do not have to generate or keep track of any new keys.
- There is no key management; users have the same permissions on the server that they do locally.
- No keys are stored on the server, so in case the server is compromised, you don't need to hunt down and remove the compromised keys.
Cons
- Users must SSH in to deploy; automated deploy processes can't be used.
- SSH agent forwarding can be troublesome to run for Windows users.
Setup
- Turn on agent forwarding locally. See our guide on SSH agent forwarding for more information.
- Set your deploy scripts to use agent forwarding. For example, on a bash script, enabling agent forwarding would look something like this:
ssh -A serverA 'bash -s' < deploy.sh
HTTPS cloning with OAuth tokens
If you don't want to use SSH keys, you can use HTTPS with OAuth tokens.
Pros
- Anyone with access to the server can deploy the repository.
- Users don't have to change their local SSH settings.
- Multiple tokens (one for each user) are not needed; one token per server is enough.
- A token can be revoked at any time, turning it essentially into a one-use password.
- Generating new tokens can be easily scripted using the OAuth API
Cons
- You must make sure that you configure your token with the correct access scopes.
- Tokens are essentially passwords, and must be protected the same way.
Setup
See our guide on Git automation with tokens.
Deploy keys
You can launch projects from a GitHub repository to your server by using a deploy key, which is an SSH key that grants access to a single repository. GitHub attaches the public part of the key directly to your repository instead of a personal user account, and the private part of the key remains on your server. For more information, see 'Delivering deployments.'
Deploy keys with write access can perform the same actions as an organization member with admin access, or a collaborator on a personal repository. For more information, see 'Repository permission levels for an organization' and 'Permission levels for a user account repository.'
Currently I am following this tutorial here: Simple Public Key Encryption with RSA and OpenSSL. I plan to transmit the RSA public key over a network to a seperate client which will encrypt a message with the generated public key. The encrypted message will then be sent back to the server for decryption. Using generated keys for encryption rsa c 1.
Pros
- Anyone with access to the repository and server has the ability to deploy the project.
- Users don't have to change their local SSH settings.
- Deploy keys are read-only by default, but you can give them write access when adding them to a repository.
Cons
- Deploy keys only grant access to a single repository. More complex projects may have many repositories to pull to the same server.
- Deploy keys are usually not protected by a passphrase, making the key easily accessible if the server is compromised.
Setup
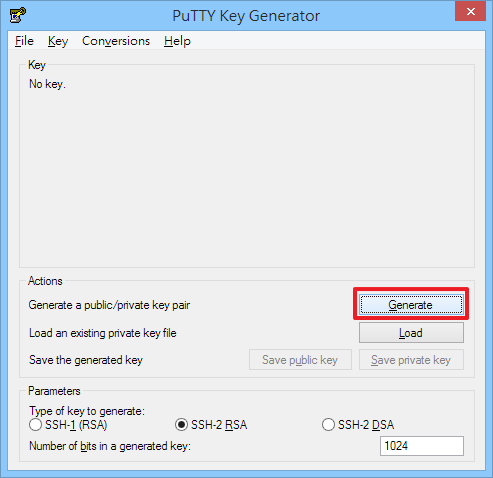
- Run the
ssh-keygenprocedure on your server, and remember where you save the generated public/private rsa key pair. - In the upper-right corner of any GitHub page, click your profile photo, then click Your profile.
- On your profile page, click Repositories, then click the name of your repository.
- From your repository, click Settings.
- In the sidebar, click Deploy Keys, then click Add deploy key.
- Provide a title, paste in your public key.
- Select Allow write access if you want this key to have write access to the repository. A deploy key with write access lets a deployment push to the repository.
- Click Add key.
Machine users
If your server needs to access multiple repositories, you can create a new GitHub account and attach an SSH key that will be used exclusively for automation. Since this GitHub account won't be used by a human, it's called a machine user. You can add the machine user as a collaborator on a personal repository (granting read and write access), as an outside collaborator on an organization repository (granting read, write, or admin access), or to a team with access to the repositories it needs to automate (granting the permissions of the team).
Tip: Our terms of service state:
Accounts registered by 'bots' or other automated methods are not permitted.
This means that you cannot automate the creation of accounts. But if you want to create a single machine user for automating tasks such as deploy scripts in your project or organization, that is totally cool.
Pros
- Anyone with access to the repository and server has the ability to deploy the project.
- No (human) users need to change their local SSH settings.
- Multiple keys are not needed; one per server is adequate.
Cons
- Only organizations can restrict machine users to read-only access. Personal repositories always grant collaborators read/write access.
- Machine user keys, like deploy keys, are usually not protected by a passphrase.
Setup
- Run the
ssh-keygenprocedure on your server and attach the public key to the machine user account. - Give the machine user account access to the repositories you want to automate. You can do this by adding the account as a collaborator, as an outside collaborator, or to a team in an organization.
This repository contains scripts for the R&D setup of OpenFlight Compute.
Monster hunter generations ultimate key quests hr 13. It's basically the online game hub, so all of the monsters and missions here are scaled for multiple players.But sometimes, there are just days when it feels like all the groups you’re joining are full of fail.
Configure Environment
Currently, this is being developed and tested on Azure.
Launch the latest Cloud Controller
Login to the controller and authorise cloud CLI tools (
az login/aws configure)Clone the cluster builder repository
Run the setup (Note: this will create an SSH keypair at /root/.ssh/id_rsa)
Update the config variables to reflect desired cloud configuration
Generate An Ssh Key Github Download
Create a Cluster
Cluster Using Default Configuration
Navigate to builder directory
Create a cluster, providing the name and public SSH key to use
Cluster Using Alternative Configuration
In some circumstances there are common deployment configurations that make constant management of one config file time-consuming and inflexible. For this reason, multiple configuration files can exist within configs/ to allow for storage of these deployment details.
Navigate to builder directory
Create a new config file
Update variables and configuration to meet your requirements
Create a cluster, providing the name and public SSH key to use
Cluster Using Password Instead of SSH Key
While less secure, this method of authorising access to a cluster may be required from time to time. In order to switch from key authorisation to password, set the AUTH variable to password in the desired config file.
Generate Ssh Key Github Enterprise
When AUTH is set to password the second argument to the build script will be used as the password instead of being used as an SSH public key.
Additional Notes
- If the variable
SSH_PUB_KEYis present in a config file then it will be used. This value will be overwritten if an SSH key is passed on the command line. - If the variable
PASSWORDis present in a config file then it will be used. This value will be overwritten if a password is passed on the command line.
Cloud Init
The build-cluster.sh script creates a cloud-init string that will be run on all the nodes, the cloud-init config:
- Adds the build machine's SSH public key to all nodes (for passwordless remote access, required for running of ansible playbook)
- Sets up configured SSH public key/password access (depending on config)
- Disables the firewall
- Disabled NetworkManager
- Sets the timezone to Europe/London
- Ensures that the cluster domain name is part of the search zone in
/etc/resolv.conf
Versioning
The version release tags align with the tags in the openflight-ansible-playbook tags.