Surrogate Key Generation In Informatica
'Hi all, I am into intial stages of my project,need to know how do I generate surrogate keys using Informatica Power Centre. Ur help would be highly appreciated. Thanks in advance. Mayuksel via informatica-l. Jul 20, 2019 Data warehouse surrogate keys are sequentially generated meaningless numbers associated with each and every record in the data warehouse. These surrogate keys are used to join dimension and fact tables. Usually, database sequences are used to generate surrogate key so it is always unique number Surrogate keys cannot be NULLs.Surrogate key are never populated with NULL.
- Feb 21, 2013 Example: If EMPNO is the key, we can keep only one record in target for the same Employee number and can’t maintain history, so we use Surrogate key as Primary key and not EMPNO. Informatica Sequence Generator: Passive and Connected Transformation; The Sequence Generator transformation generates numeric values; Use the Sequence Generator to create unique primary key values, replace missing primary keys.
- Jul 20, 2019 Surrogate keys are required if you are implementing slowly changing dimension (SCD) Disadvantages of Surrogate Key. Below are some of disadvantages of using surrogate keys in data warehouse: Surrogate key generation and assignment takes unnecessary burden on ETL framework.
- Aug 22, 2015 This Video explains how to load the data with surrogate key with out using Sequence Generator. Its very good work around. Informatica Real Time Scenario 5-Generating the Surrogate Key with out.
- Apr 20, 2006 Surrogate keys. Relational theory talks about something called a “candidate key.” In SQL terms, a candidate key is any combination of columns that uniquely identifies a row (SQL and the relational model aren’t the same thing, but I’ll put that aside for this article). The data’s primary key is the minimal candidate key. Many people think a primary key is something the DBA defines, but that’s not.
- Jun 24, 2012 A surrogate key is an auto generated value, usually integer, in the dimension table. It is made the primary key of the table and is used to join a dimension to a fact table. Among other benefits, surrogate keys allow you to maintain history in a dimension table.
A surrogate key (or synthetic key, entity identifier, system-generated key, database sequence number, factless key, technical key, or arbitrary unique identifier[citation needed]) in a database is a unique identifier for either an entity in the modeled world or an object in the database. The surrogate key is not derived from application data, unlike a natural (or business) key which is derived from application data.[1]
Definition[edit]
There are at least two definitions of a surrogate:
- Surrogate (1) – Hall, Owlett and Todd (1976)
- A surrogate represents an entity in the outside world. The surrogate is internally generated by the system but is nevertheless visible to the user or application.[2]
- Surrogate (2) – Wieringa and De Jonge (1991)
- A surrogate represents an object in the database itself. The surrogate is internally generated by the system and is invisible to the user or application.
The Surrogate (1) definition relates to a data model rather than a storage model and is used throughout this article. See Date (1998).
An important distinction between a surrogate and a primary key depends on whether the database is a current database or a temporal database. Since a current database stores only currently valid data, there is a one-to-one correspondence between a surrogate in the modeled world and the primary key of the database. In this case the surrogate may be used as a primary key, resulting in the term surrogate key. In a temporal database, however, there is a many-to-one relationship between primary keys and the surrogate. Since there may be several objects in the database corresponding to a single surrogate, we cannot use the surrogate as a primary key; another attribute is required, in addition to the surrogate, to uniquely identify each object.
Although Hall et al. (1976) say nothing about this, others[specify] have argued that a surrogate should have the following characteristics:
- the value is unique system-wide, hence never reused
- the value is system generated
- the value is not manipulable by the user or application
- the value contains no semantic meaning
- the value is not visible to the user or application
- the value is not composed of several values from different domains.
Surrogates in practice[edit]
In a current database, the surrogate key can be the primary key, generated by the database management system and not derived from any application data in the database. The only significance of the surrogate key is to act as the primary key. It is also possible that the surrogate key exists in addition to the database-generated UUID (for example, an HR number for each employee other than the UUID of each employee).
A surrogate key is frequently a sequential number (e.g. a Sybase or SQL Server 'identity column', a PostgreSQL or Informixserial, an Oracle or SQL ServerSEQUENCE or a column defined with AUTO_INCREMENT in MySQL). Some databases provide UUID/GUID as a possible data type for surrogate keys (e.g. PostgreSQL UUID or SQL Server UNIQUEIDENTIFIER).
Having the key independent of all other columns insulates the database relationships from changes in data values or database design (making the database more agile) and guarantees uniqueness.
In a temporal database, it is necessary to distinguish between the surrogate key and the business key. Every row would have both a business key and a surrogate key. The surrogate key identifies one unique row in the database, the business key identifies one unique entity of the modeled world. One table row represents a slice of time holding all the entity's attributes for a defined timespan. Those slices depict the whole lifespan of one business entity. For example, a table EmployeeContracts may hold temporal information to keep track of contracted working hours. The business key for one contract will be identical (non-unique) in both rows however the surrogate key for each row is unique.
| SurrogateKey | BusinessKey | EmployeeName | WorkingHoursPerWeek | RowValidFrom | RowValidTo |
|---|---|---|---|---|---|
| 1 | BOS0120 | John Smith | 40 | 2000-01-01 | 2000-12-31 |
| 56 | P0000123 | Bob Brown | 25 | 1999-01-01 | 2011-12-31 |
| 234 | BOS0120 | John Smith | 35 | 2001-01-01 | 2009-12-31 |
Some database designers use surrogate keys systematically regardless of the suitability of other candidate keys, while others will use a key already present in the data, if there is one.
Some of the alternate names ('system-generated key') describe the way of generating new surrogate values rather than the nature of the surrogate concept.
Approaches to generating surrogates include:
- Universally Unique Identifiers (UUIDs)
- Globally Unique Identifiers (GUIDs)
- Object Identifiers (OIDs)
- Sybase or SQL Server identity column
IDENTITYORIDENTITY(n,n) - Oracle
SEQUENCE, orGENERATED AS IDENTITY(starting from version 12.1)[3] - SQL Server
SEQUENCE(starting from SQL Server 2012)[4] - PostgreSQL or IBM Informix serial
- MySQL
AUTO_INCREMENT - SQLite
AUTOINCREMENT - AutoNumber data type in Microsoft Access
AS IDENTITY GENERATED BY DEFAULTin IBM DB2- Identity column (implemented in DDL) in Teradata
- Table Sequence when the sequence is calculated by a procedure and a sequence table with fields: id, sequenceName, sequenceValue and incrementValue
Advantages[edit]
Immutability[edit]
Surrogate keys do not change while the row exists. This has the following advantages:
- Applications cannot lose their reference to a row in the database (since the identifier never changes).
- The primary or natural key data can always be modified, even with databases that do not support cascading updates across related foreign keys.
Requirement changes[edit]
Attributes that uniquely identify an entity might change, which might invalidate the suitability of natural keys. Consider the following example:
- An employee's network user name is chosen as a natural key. Upon merging with another company, new employees must be inserted. Some of the new network user names create conflicts because their user names were generated independently (when the companies were separate).
In these cases, generally a new attribute must be added to the natural key (for example, an original_company column).With a surrogate key, only the table that defines the surrogate key must be changed. With natural keys, all tables (and possibly other, related software) that use the natural key will have to change.
Some problem domains do not clearly identify a suitable natural key. Surrogate keys avoid choosing a natural key that might be incorrect.
 Here, we shall tell you all the users about Windows 10 Product Key Generator.
Here, we shall tell you all the users about Windows 10 Product Key Generator.
Performance[edit]
Surrogate keys tend to be a compact data type, such as a four-byte integer. This allows the database to query the single key column faster than it could multiple columns. Furthermore, a non-redundant distribution of keys causes the resulting b-tree index to be completely balanced. Surrogate keys are also less expensive to join (fewer columns to compare) than compound keys.
Compatibility[edit]
While using several database application development systems, drivers, and object-relational mapping systems, such as Ruby on Rails or Hibernate, it is much easier to use an integer or GUID surrogate keys for every table instead of natural keys in order to support database-system-agnostic operations and object-to-row mapping.
Uniformity[edit]
When every table has a uniform surrogate key, some tasks can be easily automated by writing the code in a table-independent way.
Validation[edit]
It is possible to design key-values that follow a well-known pattern or structure which can be automatically verified. For instance, the keys that are intended to be used in some column of some table might be designed to 'look differently from' those that are intended to be used in another column or table, thereby simplifying the detection of application errors in which the keys have been misplaced. However, this characteristic of the surrogate keys should never be used to drive any of the logic of the applications themselves, as this would violate the principles of Database normalization.
Disadvantages[edit]
Disassociation[edit]
The values of generated surrogate keys have no relationship to the real-world meaning of the data held in a row. When inspecting a row holding a foreign key reference to another table using a surrogate key, the meaning of the surrogate key's row cannot be discerned from the key itself. Every foreign key must be joined to see the related data item. If appropriate database constraints have not been set, or data imported from a legacy system where referential integrity was not employed, it is possible to have a foreign-key value that does not correspond to a primary-key value and is therefore invalid. (In this regard, C.J. Date regards the meaninglessness of surrogate keys as an advantage. [5])
To discover such errors, one must perform a query that uses a left outer join between the table with the foreign key and the table with the primary key, showing both key fields in addition to any fields required to distinguish the record; all invalid foreign-key values will have the primary-key column as NULL. The need to perform such a check is so common that Microsoft Access actually provides a 'Find Unmatched Query' wizard that generates the appropriate SQL after walking the user through a dialog. (It is, however, not too difficult to compose such queries manually.) 'Find Unmatched' queries are typically employed as part of a data cleansing process when inheriting legacy data.
Surrogate keys are unnatural for data that is exported and shared. A particular difficulty is that tables from two otherwise identical schemas (for example, a test schema and a development schema) can hold records that are equivalent in a business sense, but have different keys. This can be mitigated by NOT exporting surrogate keys, except as transient data (most obviously, in executing applications that have a 'live' connection to the database).
When surrogate keys supplant natural keys, then domain specific referential integrity will be compromised. For example, in a customer master table, the same customer may have multiple records under separate customer IDs, even though the natural key (a combination of customer name, date of birth, and E-mail address) would be unique. To prevent compromise, the natural key of the table must NOT be supplanted: it must be preserved as a unique constraint, which is implemented as a unique index on the combination of natural-key fields.
Query optimization[edit]
Relational databases assume a unique index is applied to a table's primary key. The unique index serves two purposes: (i) to enforce entity integrity, since primary key data must be unique across rows and (ii) to quickly search for rows when queried. Since surrogate keys replace a table's identifying attributes—the natural key—and since the identifying attributes are likely to be those queried, then the query optimizer is forced to perform a full table scan when fulfilling likely queries. The remedy to the full table scan is to apply indexes on the identifying attributes, or sets of them. Where such sets are themselves a candidate key, the index can be a unique index.
These additional indexes, however, will take up disk space and slow down inserts and deletes.
Normalization[edit]
Surrogate keys can result in duplicate values in any natural keys. To prevent duplication, one must preserve the role of the natural keys as unique constraints when defining the table using either SQL's CREATE TABLE statement or ALTER TABLE ..ADD CONSTRAINT statement, if the constraints are added as an afterthought.
Business process modeling[edit]
Because surrogate keys are unnatural, flaws can appear when modeling the business requirements. Business requirements, relying on the natural key, then need to be translated to the surrogate key. A strategy is to draw a clear distinction between the logical model (in which surrogate keys do not appear) and the physical implementation of that model, to ensure that the logical model is correct and reasonably well normalised, and to ensure that the physical model is a correct implementation of the logical model.
Inadvertent disclosure[edit]
Proprietary information can be leaked if sequential key generators are used. By subtracting a previously generated sequential key from a recently generated sequential key, one could learn the number of rows inserted during that time period. This could expose, for example, the number of transactions or new accounts per period. There are a few ways to overcome this problem:
- Increase the sequential number by a random amount.
- Generate a random key such as a UUID
Inadvertent assumptions[edit]
Sequentially generated surrogate keys can imply that events with a higher key value occurred after events with a lower value. This is not necessarily true, because such values do not guarantee time sequence as it is possible for inserts to fail and leave gaps which may be filled at a later time. If chronology is important then date and time must be separately recorded.
See also[edit]
References[edit]
Citations[edit]
- ^'What is a Surrogate Key? - Definition from Techopedia'. Techopedia.com. Retrieved 2020-02-21.
- ^P A V Hall, J Owlett, S J P Todd, 'Relations and Entities', Modelling in Data Base Management Systems (ed GM Nijssen),North Holland 1976.
- ^http://docs.oracle.com/database/121/SQLRF/statements_7002.htm#SQLRF01402
- ^https://msdn.microsoft.com/en-us/library/ff878091.aspx
- ^ C.J. Date. The primacy of primary keys. From 'Relational Database Writings, 1991-1994. Addison-Wesley, Reading, MA.
Sources[edit]
- This article is based on material taken from the Free On-line Dictionary of Computing prior to 1 November 2008 and incorporated under the 'relicensing' terms of the GFDL, version 1.3 or later.
- Nijssen, G.M. (1976). Modelling in Data Base Management Systems. North-Holland Pub. Co. ISBN0-7204-0459-2.
- Engles, R.W.: (1972), A Tutorial on. CiteSeerX10.1.1.16.3195.Cite journal requires
journal=(help) - Date, C. J. (1998). 'Chapters 11 and 12'. Relational Database Writings 1994–1997. ISBN0201398141.
- Carter, Breck. 'Intelligent Versus Surrogate Keys'. Retrieved 2006-12-03.
- Richardson, Lee. 'Create Data Disaster: Avoid Unique Indexes – (Mistake 3 of 10)'. Archived from the original on 2008-01-30. Retrieved 2008-01-19.
- Berkus, Josh. 'Database Soup: Primary Keyvil, Part I'. Retrieved 2006-12-03.
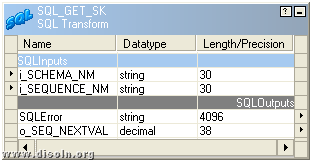
Use the surrogate key transformation to add an incrementing key value to each row of data. This is useful when designing dimension tables in a star schema analytical data model. In a star schema, each member in your dimension tables requires a unique key that is a non-business key.
Configuration
Key column: The name of the generated surrogate key column.
Start value: The lowest key value that will be generated.
Increment keys from existing sources

To start your sequence from a value that exists in a source, use a derived column transformation following your surrogate key transformation to add the two values together:
Increment from existing maximum value
To seed the key value with the previous max, there are two techniques that you can use based on where your source data is.
Database sources
Use a SQL query option to select MAX() from your source. For example, Select MAX(<surrogateKeyName>) as maxval from <sourceTable>/
File sources
If your previous max value is in a file, use the max() function in the aggregate transformation to get the previous max value:
In both cases, you must join your incoming new data together with your source that contains the previous max value.
Surrogate Key Generation In Informatica 2
Data flow script
Syntax
Example
Surrogate Key Generation In Informatica 2016
The data flow script for the above surrogate key configuration is in the code snippet below.
Next steps
These examples use the Join and Derived Column transformations.