Dsa Key Generation In Java
CkDsa dsa = new CkDsa; // Call GenKey to generate a new DSA key. // The number of bits should be at least 1024 and a multiple // of 64. Typical values are either 1024 or 2048. // DSA key generation is compute intensive and may take // a short while to complete. Boolean success = dsa. System.out.println('DSA Max key length: ' + Cipher.getMaxAllowedKeyLength('DSA')); DSA Max key length: But if you echeck the Keysize Restrictions in the JCE Providers Docs, 1024-bit is the max. Who can tell if 2048 bit private key simply not supported in Java 7?
In order to be able to create a digital signature, you need a private key. (Its corresponding public key will be needed in order to verify the authenticity of the signature.)
- ∟ RsaKeyGenerator.java for RSA Key Generation This section describes the initial draft of a RSA public key and private key generation implementation using the java.math.BigInteger class. The first step of RSA public key encryption implementation is to write a program to generate a pair of public key and private key.
- Nov 01, 2012 You post is interestnig, is there away I can create a privatre key instance via a signature given stiring? I have pub/private keys generated already KeyPairGenerator keyPairGenerator is going to createa key pair, but in my case I alrady have it and then further want to use them for signign.
In some cases the key pair (private key and corresponding public key) are already available in files. In that case the program can import and use the private key for signing, as shown in Weaknesses and Alternatives.
In other cases the program needs to generate the key pair. A key pair is generated by using the KeyPairGenerator class.
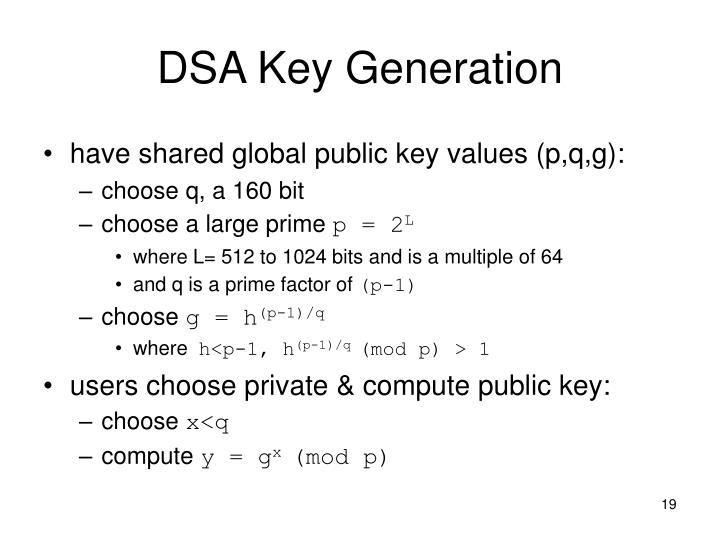
In this example you will generate a public/private key pair for the Digital Signature Algorithm (DSA). You will generate keys with a 1024-bit length.
Generating a key pair requires several steps:
Create a Key Pair Generator
The first step is to get a key-pair generator object for generating keys for the DSA signature algorithm.
As with all engine classes, the way to get a KeyPairGenerator object for a particular type of algorithm is to call the getInstance static factory method on the KeyPairGenerator class. This method has two forms, both of which hava a String algorithm first argument; one form also has a String provider second argument.
A caller may thus optionally specify the name of a provider, which will guarantee that the implementation of the algorithm requested is from the named provider. The sample code of this lesson always specifies the default SUN provider built into the JDK.
Put the following statement after the
line in the file created in the previous step, Prepare Initial Program Structure:
Initialize the Key Pair Generator
The next step is to initialize the key pair generator. All key pair generators share the concepts of a keysize and a source of randomness. The KeyPairGenerator class has an initialize method that takes these two types of arguments.
The keysize for a DSA key generator is the key length (in bits), which you will set to 1024.
The source of randomness must be an instance of the SecureRandom class that provides a cryptographically strong random number generator (RNG). For more information about SecureRandom, see the SecureRandom API Specification and the Java Cryptography Architecture Reference Guide .
The following example requests an instance of SecureRandom that uses the SHA1PRNG algorithm, as provided by the built-in SUN provider. The example then passes this SecureRandom instance to the key-pair generator initialization method.
Some situations require strong random values, such as when creating high-value and long-lived secrets like RSA public and private keys. To help guide applications in selecting a suitable strong SecureRandom implementation, starting from JDK 8 Java distributions include a list of known strong SecureRandom implementations in the securerandom.strongAlgorithms property of the java.security.Security class. When you are creating such data, you should consider using SecureRandom.getInstanceStrong(), as it obtains an instance of the known strong algorithms.
Generate the Pair of Keys
The final step is to generate the key pair and to store the keys in PrivateKey and PublicKey objects.
Key generators are constructed using one of the getInstance class methods of this class.
KeyGenerator objects are reusable, i.e., after a key has been generated, the same KeyGenerator object can be re-used to generate further keys.
There are two ways to generate a key: in an algorithm-independent manner, and in an algorithm-specific manner. The only difference between the two is the initialization of the object:
- Algorithm-Independent Initialization
All key generators share the concepts of a keysize and a source of randomness. There is an
initmethod in this KeyGenerator class that takes these two universally shared types of arguments. There is also one that takes just akeysizeargument, and uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation), and one that takes just a source of randomness.Since no other parameters are specified when you call the above algorithm-independent
initmethods, it is up to the provider what to do about the algorithm-specific parameters (if any) to be associated with each of the keys.Product key generator office. As a researcher, you are constantly juggling different roles, dealing with competing demands on your time, and coordinating not only your own activities in publishing research but also those of your collaborators–around the department and around the world.EndNote X9 is the reference management software that not only frees you from the tedious work of manually collecting and curating your research materials and formatting bibliographies, but also gives you greater ease and control in coordinating with your colleagues.
- Algorithm-Specific Initialization
For situations where a set of algorithm-specific parameters already exists, there are two
initmethods that have anAlgorithmParameterSpecargument. One also has aSecureRandomargument, while the other uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation).
In case the client does not explicitly initialize the KeyGenerator (via a call to an init method), each provider must supply (and document) a default initialization.
Every implementation of the Java platform is required to support the following standard KeyGenerator algorithms with the keysizes in parentheses:
Dsa Key Generation In Java 1
- AES (128)
- DES (56)
- DESede (168)
- HmacSHA1
- HmacSHA256